This post will not tell you how to do email encryption and digital signing with PGP (or GNU PGP), but why and to introduce some of the concepts of PGP. Hopefully without making the mistake that most documents talking about encryption make which is to get stuck into the mathematics. The intention is that this will be the first in a series of articles going through all the details necessary to run PGP. Of course the contents of this post are specific to email and email encryption, and in some places there are little white lies – for example PGP can be used to encrypt pretty much anything including emails. But first …
Why PGP ?
There are two good reasons for using PGP (or “Pretty Good Privacy”) :-
- It has a perfectly adequate level of encryption tested over many years. As it is widely used by cipherpunks, it can be considered to be reasonably safe … for now.
- If you find someone who uses encryption in email day to day, it is almost certainly going to be PGP of some kind or another. People who need to communicate with others need to have encryption standards in common, and OpenPGP is pretty much the standard in this area.
PGP has quite a long and interesting history including being classified as a munitions product (thus subject to export controls), commercialisation, and standardisation as an Internet standard. OpenPGP is the standard to which all implementations mustadhere to including the original implementation.
What Does It Do?
It encrypts emails of course! But as a consequence it also implements digital signatures.
The purpose of encrypting email is of course to encode the contents of an email message in such a way as to prevent anyone reading it other than the intended recipient. Email is normally transmitted “in the clear” between the sender and the recipient which means that anyone with access to the mail servers between the two people involved can intercept that message and read the contents. There are various methods of server-side technologies to make email more secure, but ultimately the only way of being sure that your email is safe from interception is to use end-to-end encryption which is what PGP provides.
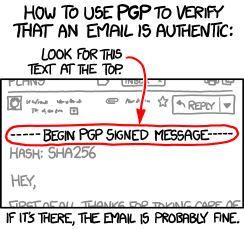
Digital signatures use the same encryption technology to sign a message to give a high level of confidence that a certain person wrote a particular message and that the message has not been modified in any way.
Public and Private Keys
The key (sorry!) thing about public/private keys in cryptography is that it just works providing that :-
- You choose a good pass phrase for your private key, and keep it safe.
- You keep your private key very, very private.
To encrypt an email to someone, you would use the recipient’s public key to perform the encryption; at which point only the recipient’s private key can be used to decrypt the message.
Digital signing works the other way around – you sign a message with your private key and anyone who has your public key can verify that your message was sent (and not modified) by you.
As you can see, anyone who manages to obtain your private key is able to not just intercept and read mail intended for your eyes only, but also to send out email that purports to come from you in a way that nobody can determine it is forged.
Obtaining Public Keys
Before you can send someone encrypted email, you need to obtain their public key. There are basically two methods to get someone’s public key :-
- Obtain their public key directly from them. Ideally in person to ensure that someone isn’t impersonating them on email … whilst this may seem unlikely, people who worry about encryption do worry about this sort of thing.
- Alternatively from a public key server which holds the public keys of anyone who has submitted it for public use.
The public key will be a plain text file with rather inscrutable contents :-
-----BEGIN PGP PUBLIC KEY BLOCK----- Version: GnuPG v2.0.19 (GNU/Linux) mQGiBDypfKARBADbpVbuMSGLLZaskm9IGK9wH2jAX4jhk/J7upqt9/iz8wzZR/tk (Lots of lines removed) luVqmVGLLv/NxAR76fFRe2Xyxpv5LS+zVkNygVBNS8sveWBxxbeu4aN1N00g20Vt +r3heAfrmzBT1ABMp5CQ/p6XgFXO+D8zUiVpLpbT8b3Z7j5ZRHt5VME= =LSDA -----END PGP PUBLIC KEY BLOCK-----
Of course it isn’t usual to see something like this as it is usual to use applications to deal with keys. But if you encounter a file with contents like this, it is usual to import it into some application dealing with PGP.
Trust
At one level, the amount of trust you may have in any PGP public key should be determined by the method you used to obtain the key. Perhaps in order it would be :-
- Public key file obtained by visiting someone’s desk and have them copy their public key to your USB stick.
- Obtained via a well-known key server across the Internet.
- By downloading their public key from their web server.
It is possible to obtain an extra level of trust – which is also called a web of trust. This basically works by people signing other public keys to add levels of trust to a public key – they confirm they know that this public key belongs to the person in question.
The more people have signed a public key, the more confidence you have that it is genuine.
