Strange as it may seem, if you have a certain type of wireless mouse you may be vulnerable to an attacker being able to inject keyboard keystrokes into your computer; with this they are able to do just about anything you can imagine (and a fair bit you cannot) to your computer and use access to your computer to spy on your activities.
Now this attack does require physical proximity. The advertised range of the vulnerable devices is 10m, and an attacker could well be using an external antenna to extend that considerably, so physical proximity is not impossible.
The main vulnerable device are the Logitech family of wireless mice and keyboards – basically anything using the Unify wireless dongle :-
Whilst the problem may have been fixed in the newest devices, it makes sense to assume you are vulnerable with any device purchased any time before 31st March, 2017 (older devices can stick around on shelves a long time).
To fix the problem merely requires a firmware update, but who thinks of checking whether their mouse needs a firmware update? And how frequently?
The firmware update is relatively easily applied, and can be applied with all of the major desktop operating systems – Windows, OSX, and Linux.
Direct Updates (Temporary)
Unfortunately it would appear that Logitech have broken their update mechanisms by re-vamping their websites. As a temporary measure, it is possible to download the update directly: https://community.logitech.com/s/question/0D531000058b3B7CAI/logitech-response-to-research-findings.
As a side effect, the update mechanisms below will fail to identify outdated versions. If your firmware version does not end in ‘029’ or ‘030’ (or later), then you need an update.
Updating the Firmware with Windows (and OSX)
The process of updating the firmware with OSX is as similar to updating with Windows, that repeating the instructions with OSX screen shots instead of Windows screen shots would be unnecessarily repetitive.
To start with, you will need to download and install the Logitech software (http://support.logitech.com/en_us/software/unifying). Once installed open it :-
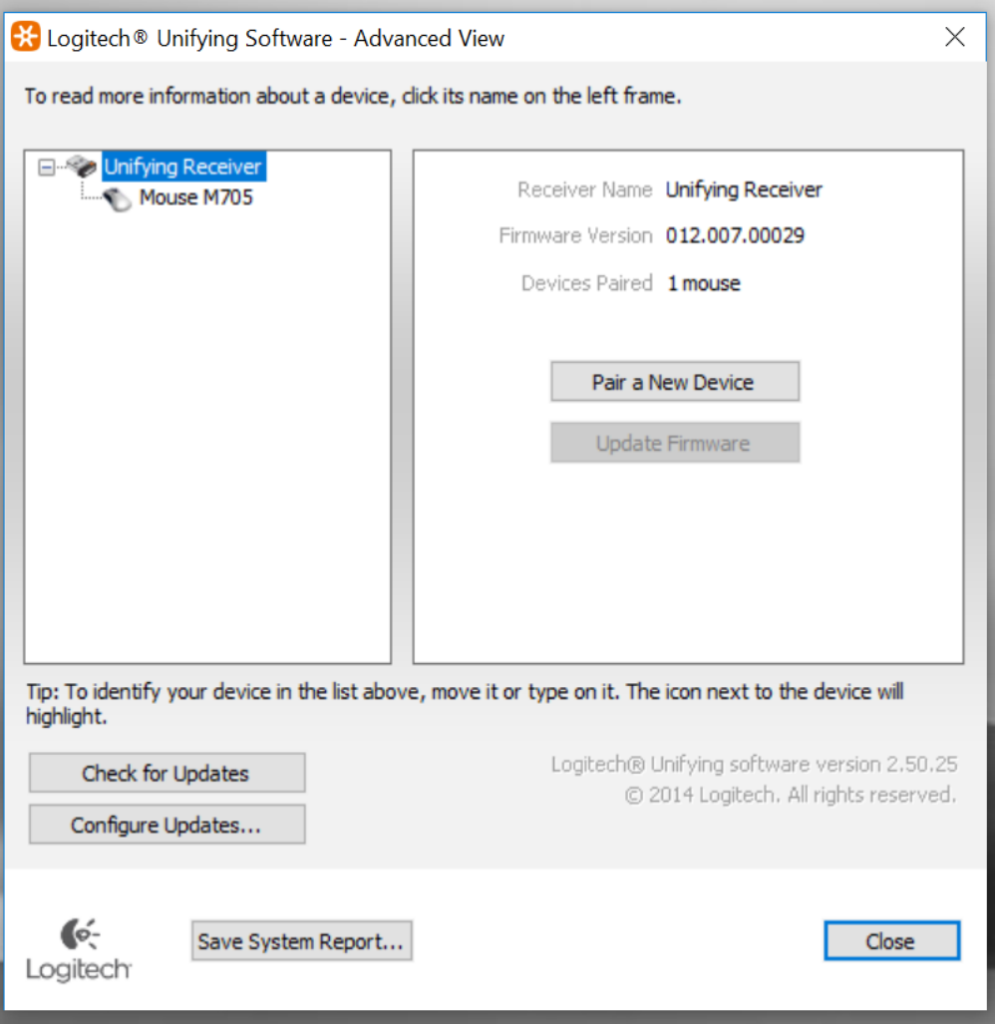
Click on the “Advanced” option :-
At this point, click on “Check for updates” to ensure that the software’s idea of what the latest firmware is reflects the latest changes. Then for each of the devices listed in the left hand side (including the “Unifying receiver”), click on the “update firmware” button if it is not greyed out.
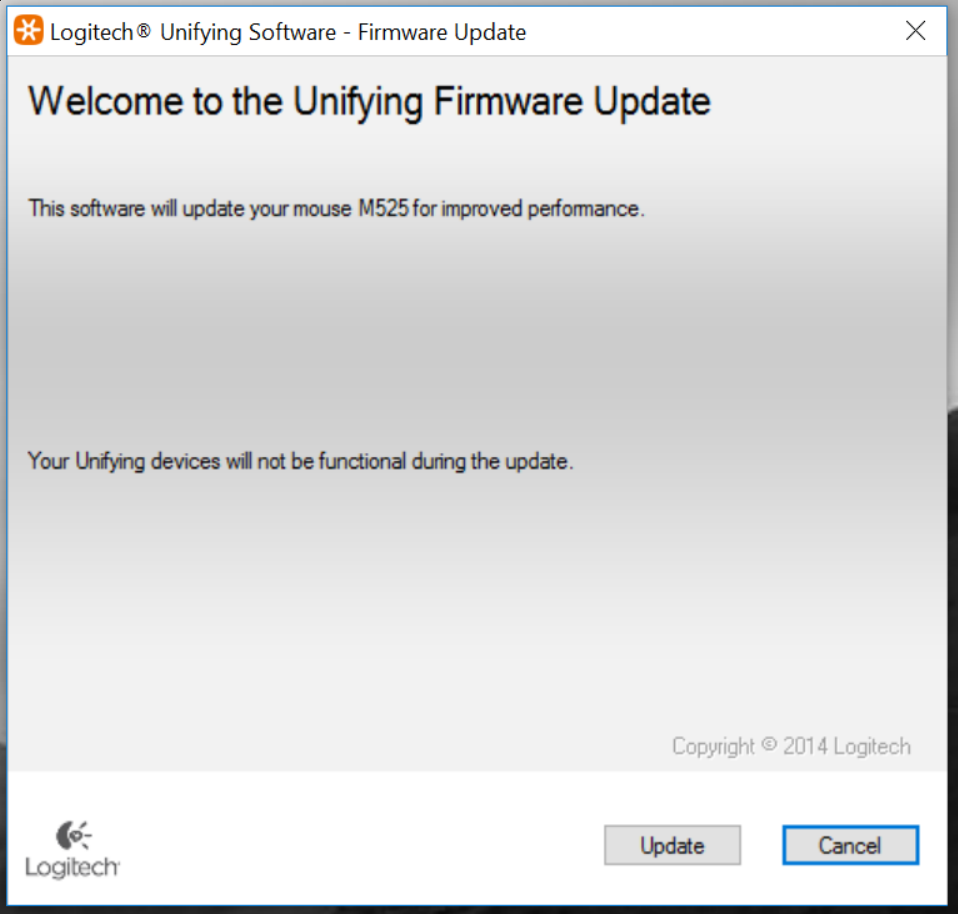
Once clicked, the screen will show :-
(Yes I have changed mice)
Simply click “Update”, and you will then be asked to turn off your mouse and turn it back on again.
Repeat this process for all of the entries in the “tree” of devices (including the wireless dongle itself).
Updating the Firmware with Linux
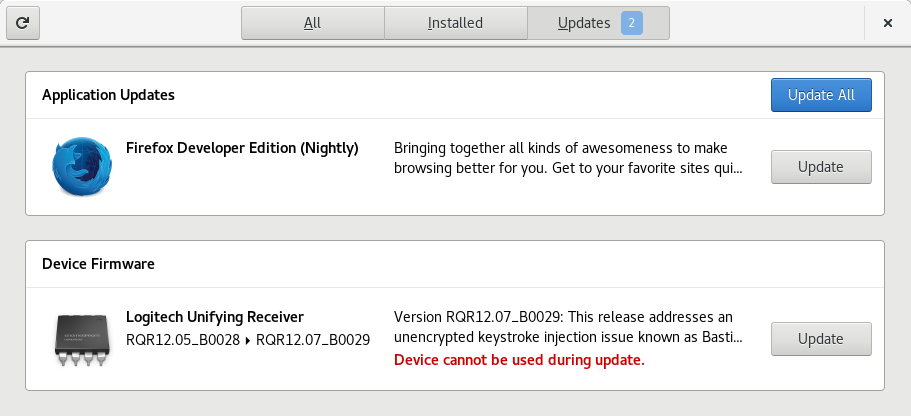
If you just happen to be running Fedora Core 26 (or Ubuntu 17.10), the firmware updates may show up automatically within GNOME Software where the operating system updates also show up :-
If you wish to do this the manual way, you can open up a terminal and running the following commands :-
$ sudo fwupdmgr refresh $ sudo fwupdmgr update
With the exception of the diversion into geek-land, this is how firmware updates should be managed – one central place to get and apply updates without having to know that your mouse needs a firmware update.
Having said that, only two major manufacturers (Logitech and Dell) have currently signed up to this piece of Linux.