One of the questions that arises from time to time is just how often do we get scanned by some kind of attacker looking for vulnerabilities?
This is a bit of a tough question to answer as it involves looking into why scans are performed, and our firewall doesn’t yet have the ability to ask an “attacker” why they are doing what they are doing. There are many different reasons why our network may be scanned :-
- Scans looking for vulnerabilities.
- Scans from monitoring sites looking for specialised vulnerabilities such as NTP, DNS, chargen, etc. These scans are looking at the size of the problem rather than trying to use the vulnerability.
- Scans from network monitoring sites and/or researchers looking at how big the Internet is.
- Random “noise” from typos, etc.
Of course there is no easy way to determine the proportions, but let us assume that a 1/4 of all scans are malicious.
But back to the original question: How often do we get scanned?
By taking an unused network – one that has never been used or allocated – we can use the firewall logs to look at “attackers” trying to connect to hosts on these networks. For one day (Sunday 26th January, 2014), this amounted to some 41,154 connection attempts.
But a single “attacker” may connect to multiple addresses within this network, so how many unique “attackers” probed something on the unused network? For the same date, it was 3,218.
Using our guess of 1/4 of those were malicious scans looking for vulnerabilities, we had 805 unique attackers on the 26th January. But is this some kind of exceptional day?
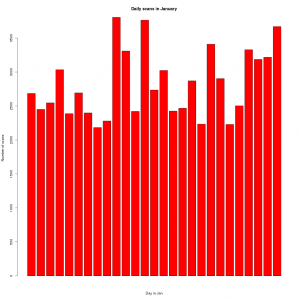
To determine that we need to look at the number of scans over the whole of January :-
| Day of January | Number of scans |
|---|---|
| 01 | 2686 |
| 02 | 2451 |
| 03 | 2547 |
| 04 | 3035 |
| 05 | 2388 |
| 06 | 2694 |
| 07 | 2399 |
| 08 | 2184 |
| 09 | 2280 |
| 10 | 3806 |
| 11 | 3310 |
| 12 | 2422 |
| 13 | 3764 |
| 14 | 2736 |
| 15 | 3024 |
| 16 | 2426 |
| 17 | 2468 |
| 18 | 2871 |
| 19 | 2234 |
| 20 | 3410 |
| 21 | 2904 |
| 22 | 2230 |
| 23 | 2503 |
| 24 | 3329 |
| 25 | 3187 |
| 26 | 3218 |
| 27 | 3670 |
So, no it wasn’t exceptional – we really do see thousands of scans per day.